Blogs.
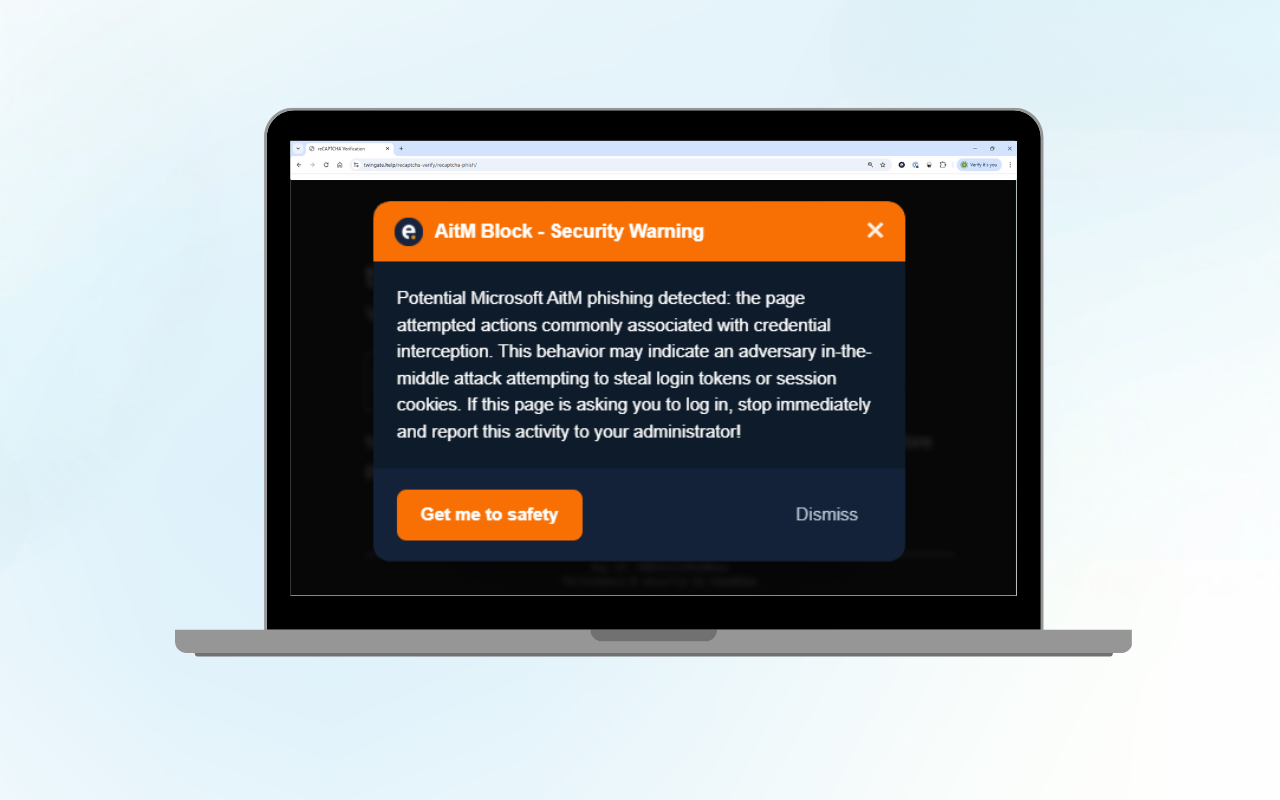
Microsoft 365 AitM Phishing Protection: Free Browser Extension
Adversary-in-the-Middle (AitM) phishing is a rapidly growing threat that can...
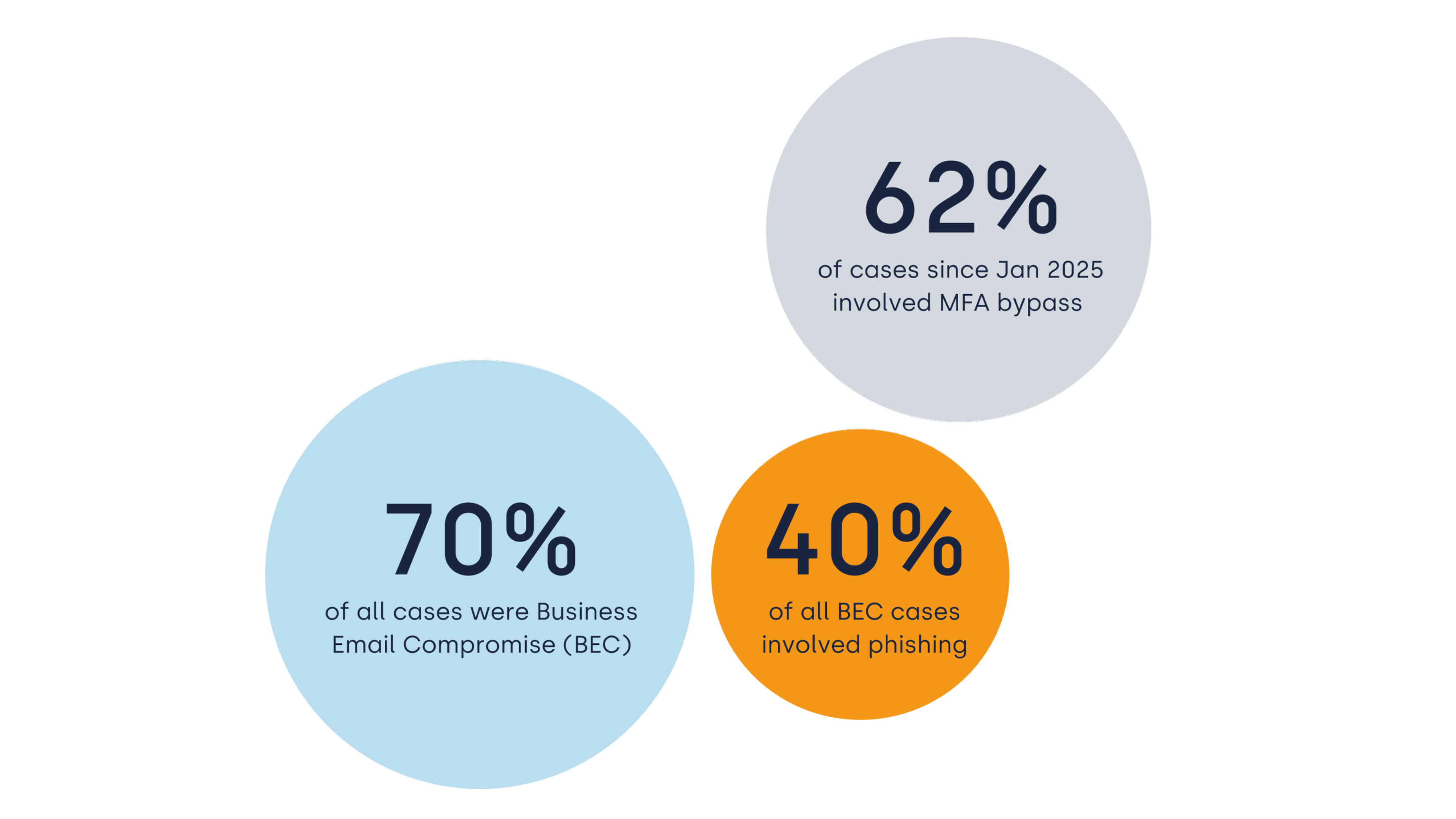
Cyber Incidents in Europe 2026: Identity-based Attacks and the Impact of MDR
Cyber incidents across Europe are accelerating. They are happening more often,...
The State of Incident Response 2026: Insights from 630 Investigations
Eye Security analysed 630 anonymised cybersecurity incidents across Europe...
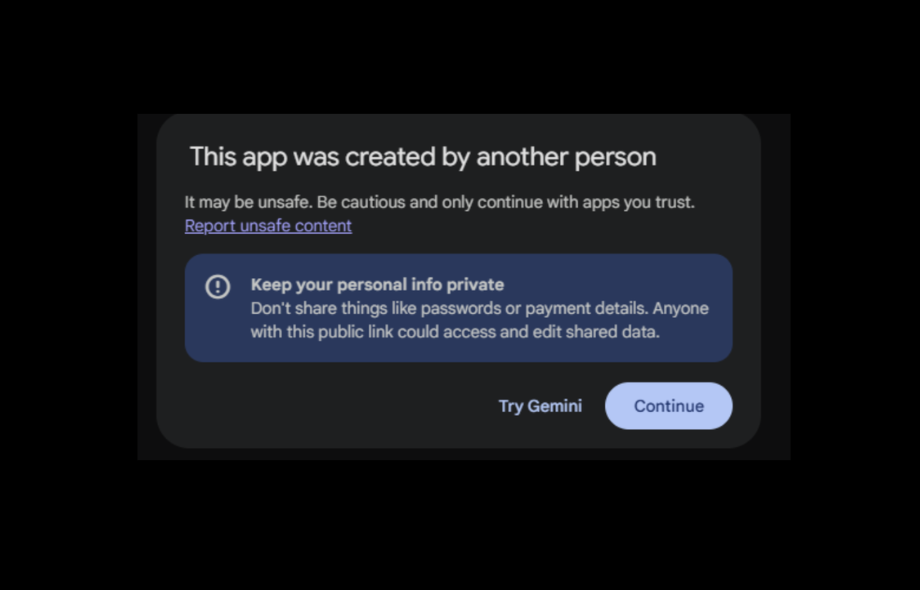
From Helper To Risk Factor: Why AI Canvases Deserve Executive Attention
Eye Research demonstrated that a shared AI canvas can convincingly imitate...


Battling Shadow AI: A Practical Tool for CISOs
Generative AI is transforming how businesses operate. Tools such as ChatGPT,...

When Business Email Compromise Nearly Costs a Million: An Incident Response Story
Business Email Compromise (BEC) remains one of the most damaging yet...

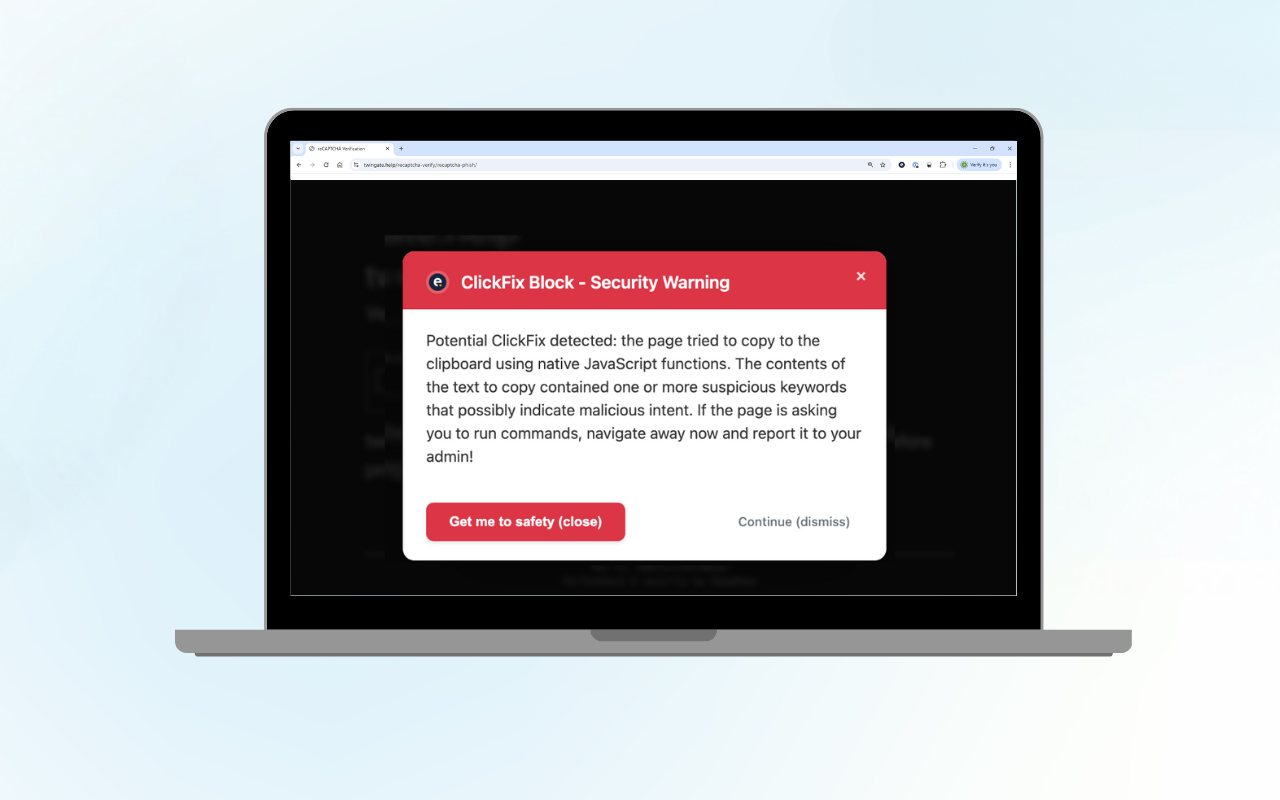
ClickFix Block: Protect Your Organisation from Fake CAPTCHA Attacks
Curious about the technical details? Read our technical blog on ClickFix Block....


Hours from shutdown: How a Logistics company escaped ransomware just in time
This is a real incident Eye Security investigated at Move Intermodal. The...
Retail Giants Breached: What the M&S, Harrods & UNFI Attacks Mean for Your Cyber Defences
A surge of high-impact cyberattacks is shaking the retail sector, exposing...

Sneaky 2FA: Use This KQL Query to Stay Ahead of the Emerging Threat
At Eye Security, we constantly seek out new threats and detection methods to...

