Blogs.
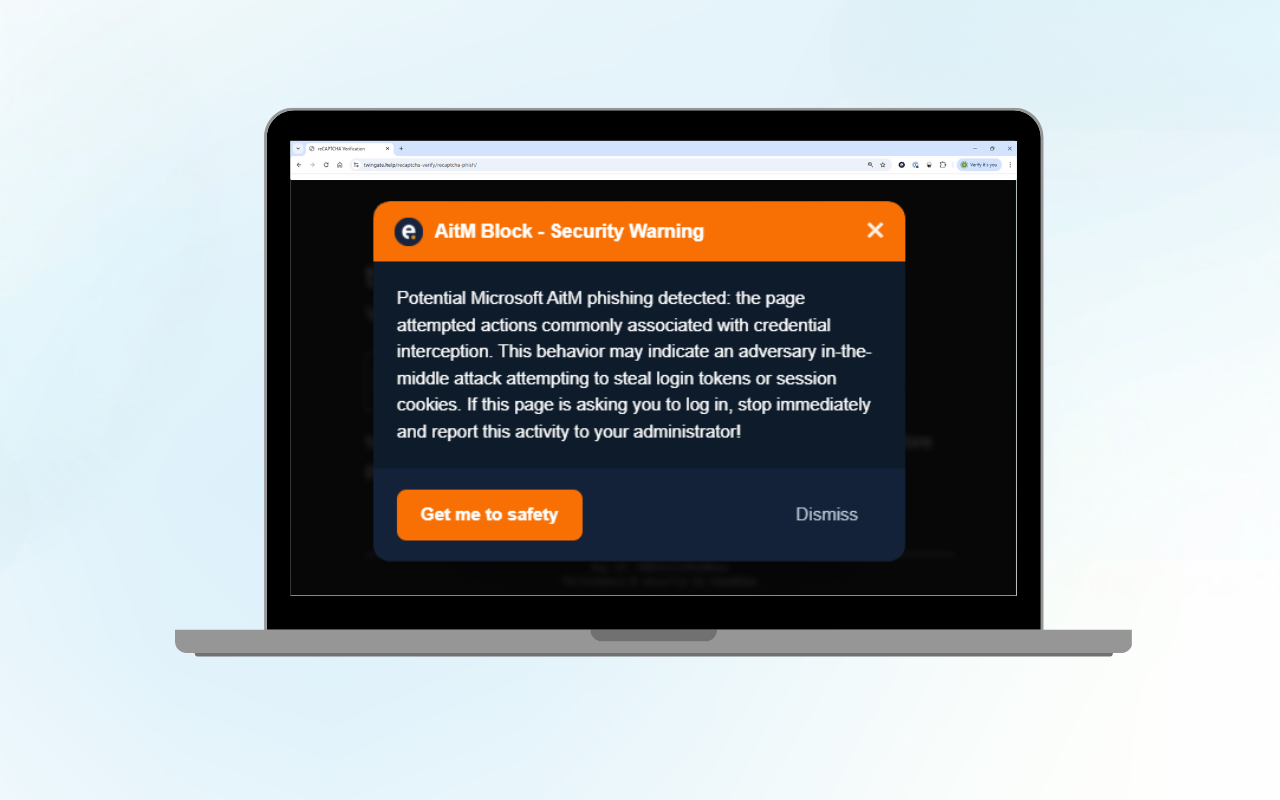
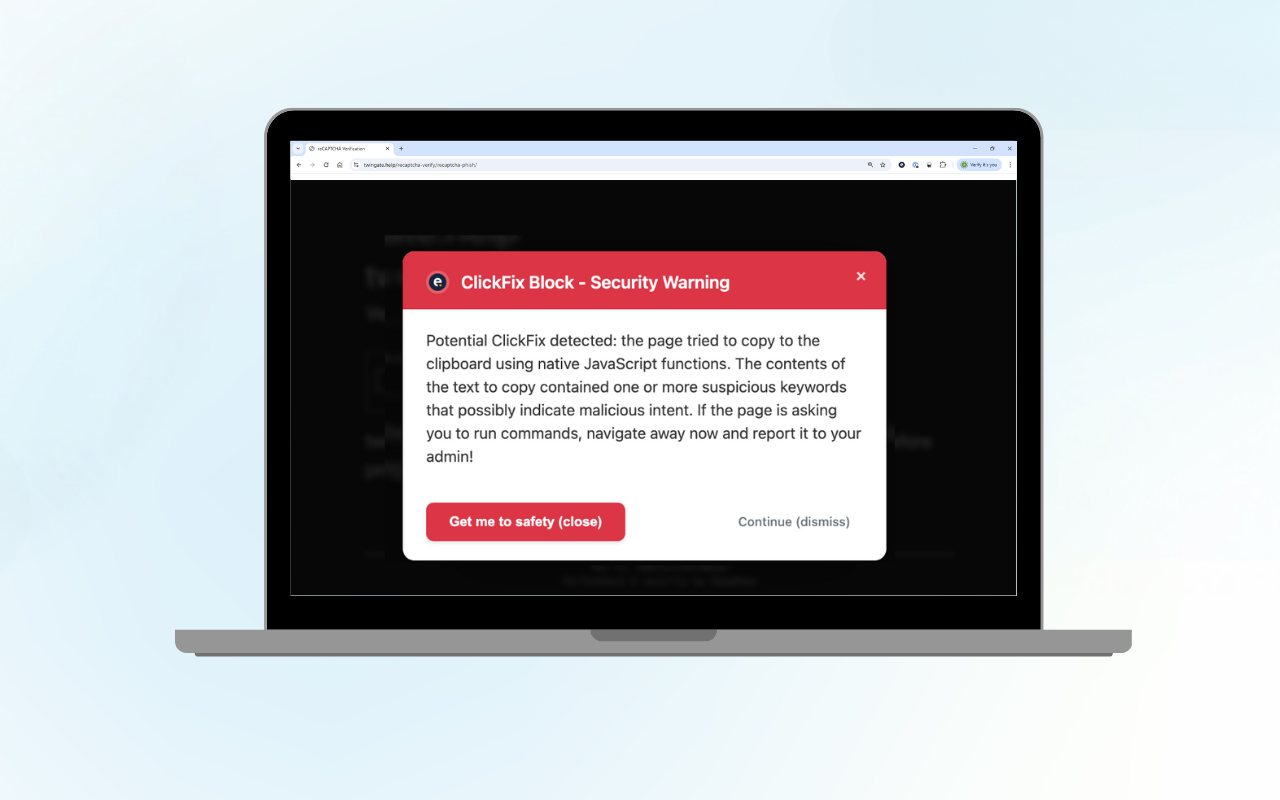
Microsoft 365 AitM Phishing Protection: Free Browser Extension
Adversary-in-the-Middle (AitM) phishing is a rapidly growing threat that can...
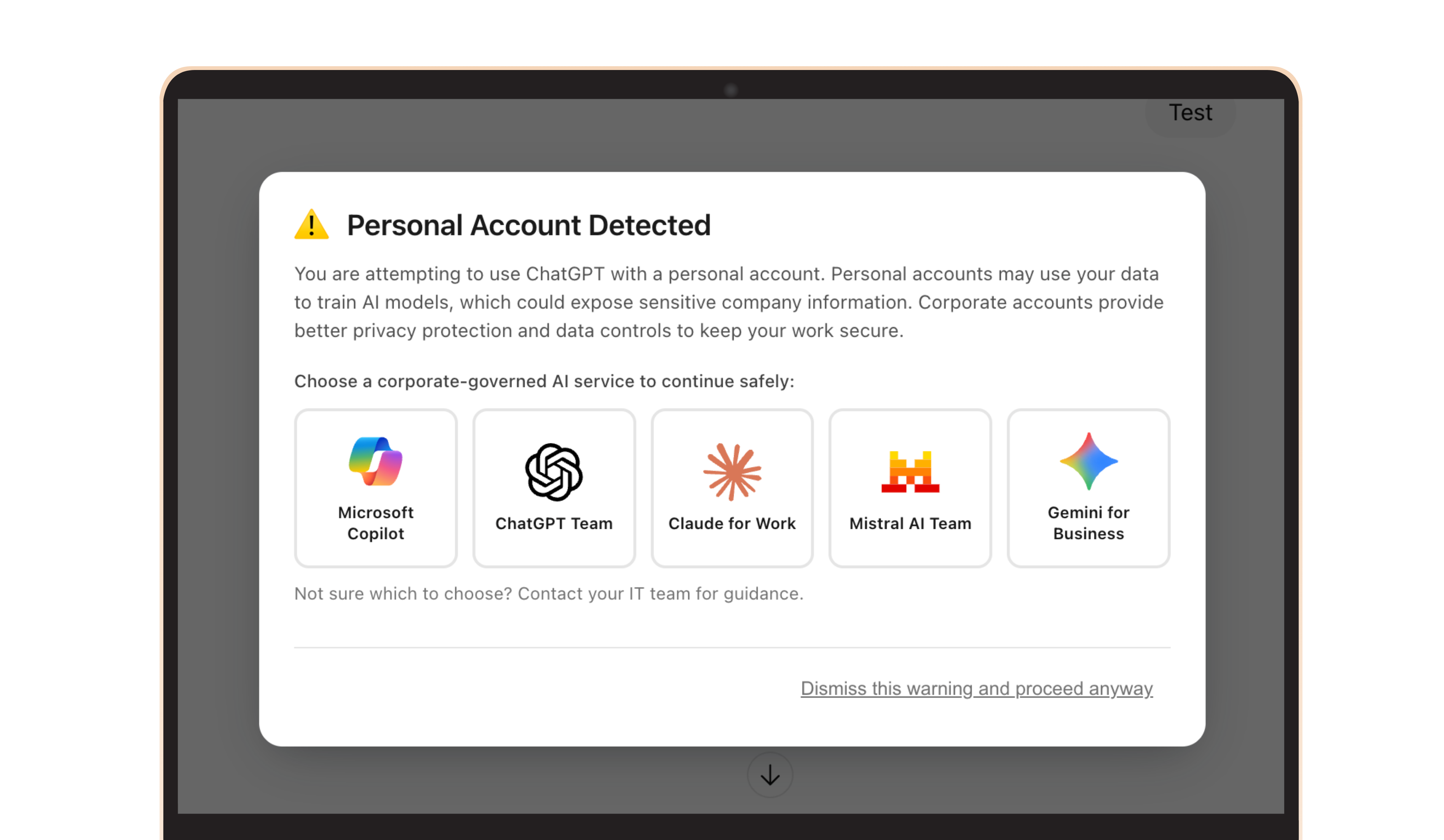
Shadow AI Is Leaking Enterprise Data: Here Is How to Prevent It in the Browser
Employees are leaking sensitive data into personal ChatGPT, Claude and Gemini...

The 90-Day Blind Spot: What Your Security Tools Are Not Telling You
You have endpoint protection. You have monitoring. You have a partner watching...
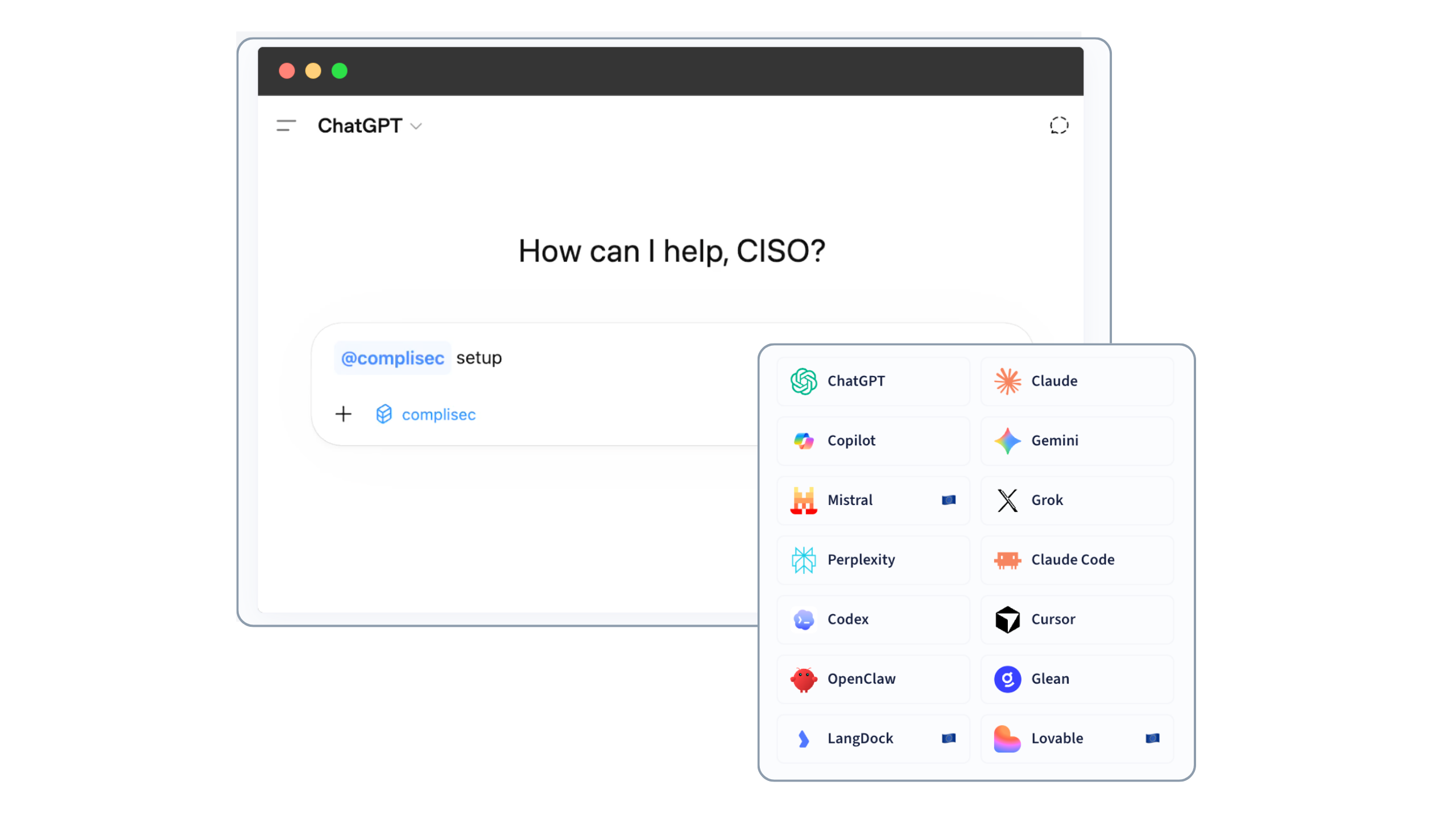
Introducing complisec: Giving AI Agents the Context to Know What They’re Allowed to Do
AI agents are already writing code, processing data, and automating internal...

A new paradigm to extinguish cyber risk for good: 24/7 protection connects with cyber insurance
...

Eliminating cyber risk for your clients together
Businesses built on partnership In the relatively short time we’ve been in...
Product Update: Demo Portal
In this blog, we sit down with Anne Postma, our Product Manager, to discuss the...


Product Update: Vulnerability & Threat Hunting
In this blog, we interview Robbin Begeer, Product Manager at Eye Security,...
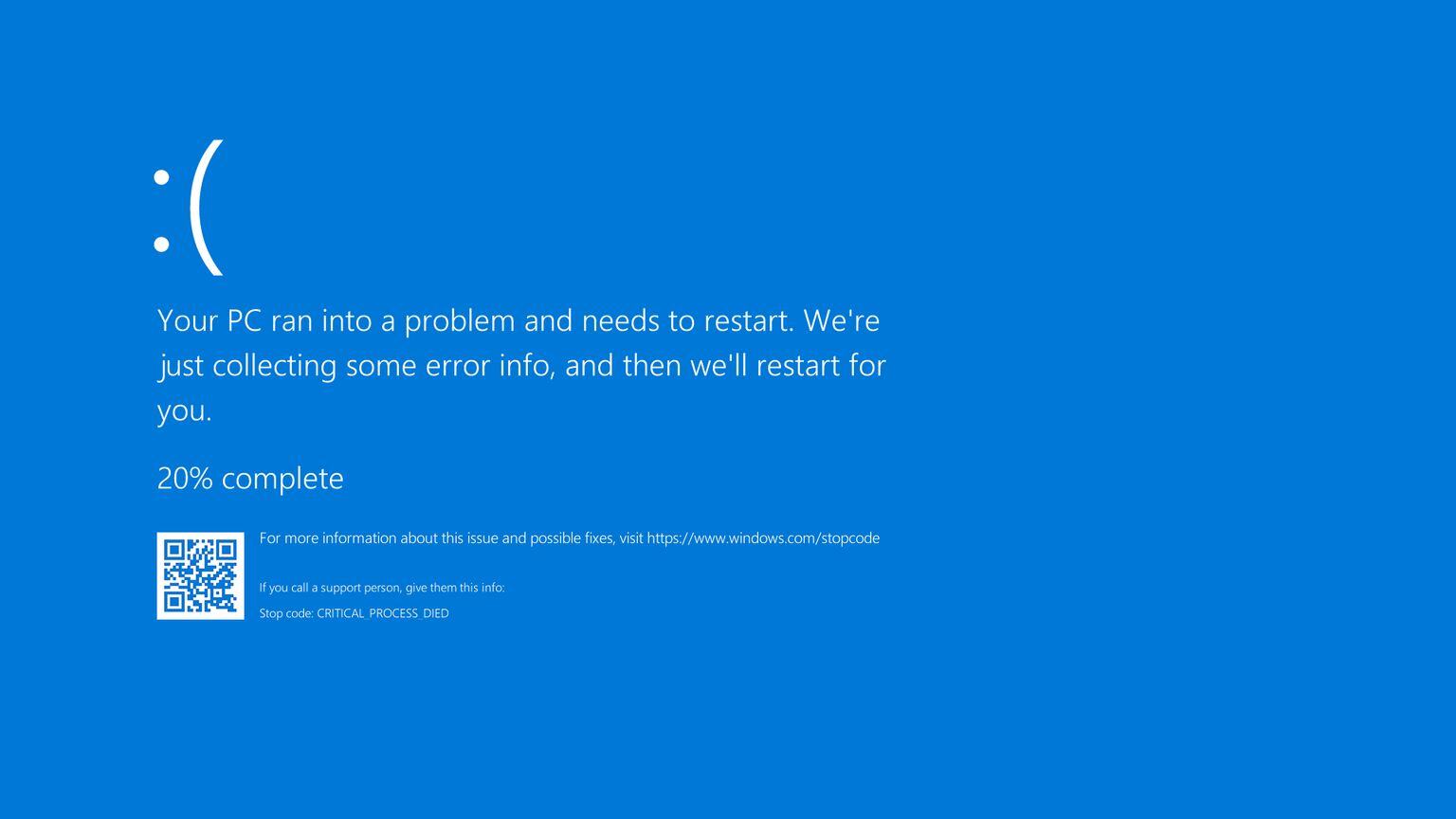
CrowdStrike Falcon and Microsoft blue screen issue updates
Last updated: July 30th at 00:00 CEST In this blog, we provided real-time...

When it comes to cybersecurity, insurers set the bar high
The insurance market is now aware that cyber risk is difficult to manage and...

Cyber insurance: your safety net in an increasingly risky world
To minimise the impact of a cyber incident, preventive security measures must...
 Bas van den Berg
Bas van den Berg
