Supply chain cyber risk has become one of the defining security issues of this era, not because it is new, but because it now moves faster than most organisations can see, interpret, and contain. The breach may start elsewhere: a software vendor, a managed service provider, a booking platform, a logistics partner, or a shared cloud service. But the operational damage, regulatory pressure, and loss of trust land squarely on your desk.
This is what makes supply chain incidents so difficult to manage and contain. They bypass the neat boundaries that still shape too many security programmes. Many organisations still organise cyber risk around assets they own directly, systems they administer, and controls they can test themselves. Threat actors do not think that way. They think in terms of access, leverage, and speed. They look for the point in an ecosystem where one compromise can create many victims.
This is why supplier-related incidents now deserve the same executive attention as ransomware readiness, identity security, and business continuity. The relevant question is no longer whether your supplier security questionnaire is complete. It is whether you could detect, contain, investigate, and report a third-party incident quickly enough to protect your business when the disruption starts outside your perimeter.
Recent field experience points to the same conclusion. Organisations are not failing because they have never heard of supply chain risk. They are failing because they still treat it primarily as a procurement issue, not as an incident response reality.
Why supply chain attacks are so difficult to manage?
Video 1. A single compromise can take down entire ecosystems.
A supply chain attack succeeds by abusing trust that already exists. That trust may be technical, operational, or human. It may be a remote management connection from a service provider, a software update mechanism, a shared identity, a synced data feed, or a routine business workflow that nobody thinks of as security-relevant until it becomes the attack path.
Supplier-related incidents are hard not because of one single control gap, but because they combine technical blind spots, operational dependencies, and ambiguity in ownership. These attacks often arrive through trusted channels. They can look like legitimate activity and can spread before internal teams even agree on whether the problem is theirs. By the time someone confirms the scope, the threat actors may already have moved downstream, exfiltrated data, or disrupted business critical systems.
This is also why traditional prevention logic breaks down. If a supplier uses legitimate credentials, if a partner account is already authorised, or if malicious activity is delivered through a real platform that employees rely on every day, many conventional controls will not stop the initial action. Defence still matters, but preparedness matters more.
What is a supply chain attack?
At its core, a supply chain attack is a compromise of a trusted third party to reach the real target or to create impact at scale. That definition matters because it reveals two distinct models that organisations need to prepare for.
Targeted supply chain compromise
In the first model, the threat actor wants a specific organisation but decides that attacking it directly is too difficult or too expensive. So they pivot to a weaker vendor, consultancy, service provider, or software supplier that has access to the real target. This model is especially attractive when the end target is well defended and the threat actor is patient, well resourced, and strategic.
In these cases, the supplier is not the end goal but the route in.
Mass downstream attack
The second model is the one that should concern most businesses most of all. Here, the threat actor compromises a supplier precisely because that supplier connects to many customers at once. One breach becomes ten. Ten become a hundred. Why extort or disrupt one company if you can leverage a single provider to affect an entire customer base?
This is the model that creates systemic damage. A breach at a managed service provider, a remote management platform, a file transfer product, or a software distribution mechanism can become an instant multiplier of impact. It also creates confusion at scale, because every downstream customer starts from the same urgent questions at the same time. Are we affected. What data was exposed. What systems are at risk. Who owns the response.
Why organisations still get breached through the supply chain
Video 2. The initial attack vectors are still fairly trivial. The example of voice phishing.
The initial access methods are rarely exotic. For the most part, threat actor are after identity and trust. Stolen credentials remain a common entry point. So do weakly protected remote access tools, exposed internet facing applications, poor patch discipline, and social engineering. Email compromise still works. Voice phishing still works. Shared administrative access still creates risk. Identities remain central because attackers increasingly prefer logging in over breaking in. The difference in supply chain attacks is not the means. It is the starting point and the resulting blast radius.
A threat actor may not care about a smaller supplier on its own. But if that supplier has a trusted route into larger clients, handles sensitive data, or supports critical business functions, the attacker has found leverage. In practice, this means that relatively ordinary weaknesses can produce extraordinary consequences when they exist inside the wrong organisation at the wrong point in the chain.
That is also why patching debates often miss the point. The right question is not whether it is safer to stay on an older version. It is whether the organisation can patch rapidly and assess exposure. But patching alone is not enough. If a newly disclosed vulnerability affects an internet facing system, organisations should also assess whether compromise may already have occurred in the window between disclosure and remediation. A patch closes the door. It does not tell you whether someone already came through it.
The real business risk: operational disruption and decision paralysis
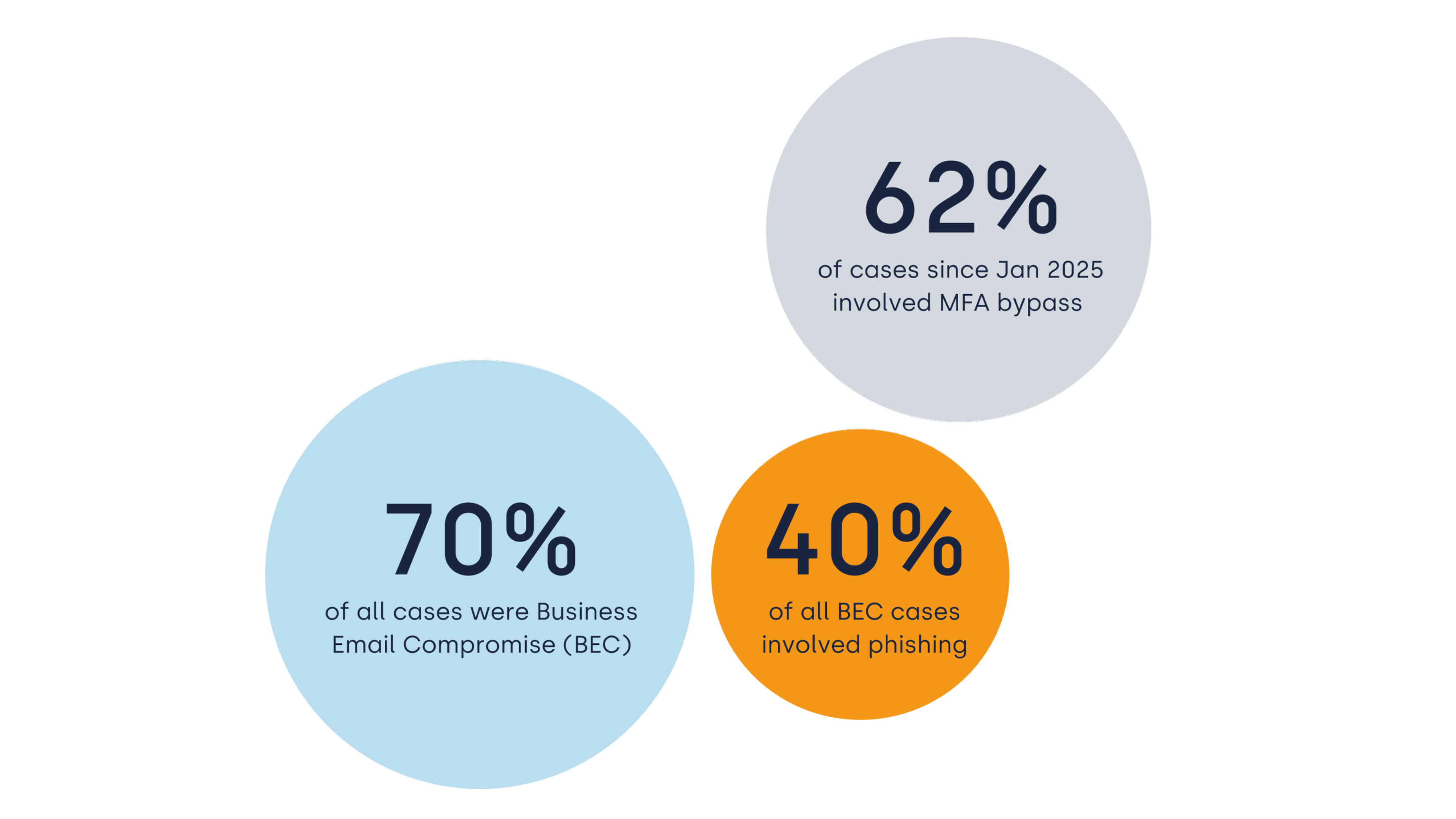
In our survey, respondents were asked about their greatest concern in a supplier related cyber incident. 60% of respondents named disruption to operations and lack of visibility into what happened.
The split is revealing. It captures the two sides of modern cyber crisis. First, business leaders fear interruption. Second, they fear uncertainty. They do not know what the supplier could access, what data moved where, or whether the incident triggers reporting obligations. This uncertainty actively slows containment, complicates legal and regulatory decisions, and damages credibility with customers and partners.
That combination is what makes supply chain incidents destabilising. The organisation is under pressure to act fast, but the facts are incomplete because the breach began in someone else’s environment.
The visibility problem that most companies underestimate
One of the clearest findings from our poll concerns data access visibility. When asked how confident they were that they could quickly determine what data a supplier can access in their environment, only a small minority expressed high confidence. Most respondents said they were only somewhat confident, not very confident, or had no visibility at all.
Many organisations know which suppliers are commercially important. Fewer know which suppliers are technically integrated. Fewer still can quickly map which data each supplier can read, modify, export, or influence. That becomes a problem during an incident. If a supplier is compromised and you cannot rapidly identify the systems, accounts, and datasets involved, you lose precious time.
A mature organisation should be able to answer five questions quickly when a supplier incident breaks:
-
which identities are involved,
-
which systems are connected,
-
which business processes depend on the supplier,
-
which data can the supplier access,
-
which decisions must be made in the first hours.
Too many companies cannot answer even two of those questions without scrambling across procurement, IT, legal, and business teams.
Case studies show the same pattern again and again
The details vary, but the pattern is consistent.
Video 3. Case study: how a compromised MSP account enabled lateral movement across multiple customer environments
Managed Service Providers (MSP) as force multipliers
A managed service provider can become the perfect pivot point for an attacker. If the provider is compromised, threat actors may inherit remote access, administrative pathways, or management tooling across multiple customer environments. In incidents like these, the breach is no longer confined to the provider. It becomes an ecosystem event.
We have seen scenarios where malicious activity was detected first in a downstream client environment, only to reveal that the originating issue was the service provider itself. In other cases, a vulnerable application in one customer environment became the bridge to a provider’s management network, and from there to additional customers. A weakness that looks local turns systemic the moment segmentation, access control, or identity boundaries fail.
Trusted platforms used for fraud at scale
Another pattern is the compromise or abuse of trusted platforms that handle customer data and transactional workflows. In hospitality and retail-related cases, attackers have leveraged access to booking systems or return processing chains to send convincing phishing messages that appeared entirely legitimate. The messages referenced real booking details, correct dates, accurate order information, and expected business processes. Victims were were responding to a trusted workflow that had been weaponised.
Why supply chain risk is now a board-level issue
Supply chains were optimised for efficiency, speed, and scale. Cyber resilience was rarely the primary design principle. That mismatch now defines the risk landscape.
A supplier breach can trigger operational disruption, legal exposure, customer communications, insurance claims, executive decision making, regulatory reporting, and reputational damage within hours. No single technical team can manage all of that alone. Yet many organisations still leave supplier cyber risk fragmented across procurement questionnaires, compliance checklists, and occasional vendor reviews.
In our webinar survey, respondents were asked whether it would be clear who leads the response if a supplier were breached today. 88% said responsibilities would only be partly clear. 12% said ownership would be unclear altogether. This is a serious warning sign. If leadership and authority are ambiguous at the start of a supplier related incident, recovery slows and confusion spreads.
In a real incident, the first questions are:
-
who can authorise containment,
-
who decides whether a supplier connection is severed,
-
who handles customer communication,
-
who assesses regulatory timelines,
-
who owns evidence preservation.
If these questions are unresolved when the breach occurs, the organisation is already behind.
What well-prepared organisations do differently
Prepared organisations do not assume they can prevent every supplier related incident. They design for fast response when prevention fails.
In most supplier breaches, the first delay comes from ownership. Security waits for confirmation. The business waits for direction. That delay is where the attack spreads.
Establish clear incident ownership
You must be able to coordinate technical response, legal review, communications, business continuity, and supplier engagement without confusion about who is in charge.
Test for supplier scenarios, not just general incidents
A striking result from our survey was that 50% of organisations have not tested their incident response plan for a supplier-related breach scenario in the past year. This matters because supplier incidents behave differently:
-
the facts may be incomplete,
-
the supplier may not share information fast enough,
-
or the operational decisions may affect contracts, customers, and third parties immediately.
Testing should reflect that complexity. Tabletop exercises should include third-party compromise, uncertain scope, data access questions, and time pressured reporting decisions.
Build evidence readiness before the crisis
Incident response is also about establishing facts. Centralised logs, durable telemetry, access records, and structured timelines matter enormously when the incident begins elsewhere. Without evidence, organisations cannot determine what happened, prove what did not happen, or support regulatory reporting with confidence.
Classify suppliers by operational criticality and access
Not all suppliers carry the same risk. The most mature organisations focus not only on who is commercially important, but on who can disrupt operations, access sensitive data, or create downstream trust abuse. They treat supplier mapping as a practical response capability, not just a governance exercise.
People, process, and technology still decide the outcome
Video 4. Don't chase perfection. Assume breach and bolster your defences.
No framework or certification can remove the need for execution. In the end, readiness still comes down to people, process, and technology.
On the people side, roles must be defined under pressure. Executives need to understand the decisions that only they can make. Procurement, IT, security, legal, and communications need a shared operating model.
On the process side, escalation paths must work outside office hours. Regulatory timelines must be understood in advance. Supplier engagement procedures must exist before the first emergency call.
On the technology side, organisations need 24/7 detection and response, strong identity controls, least privilege, segmentation, and visibility that extends beyond real time into historical investigation. Threat actors increasingly exploit valid accounts and legitimate pathways. That means organisations need not only alerts, but containment capabilities that can move quickly when those signals appear.
The strategic shift: from supplier assurance to incident readiness
Many organisations still anchor supply chain cyber risk in audits, questionnaires, and annual reviews. Those activities still have value, but they are not enough. They create a picture of declared posture, not actual response capability under stress.
The strategic shift now required is simple to describe, even if harder to implement. Move from supplier assurance alone to supplier incident readiness.
That means asking harder questions. If this supplier is compromised tomorrow, what breaks first. What data is exposed. Which identities could be abused. How would we know. Who acts. What can we isolate. What must we report. How fast can we answer those questions with evidence.
The first hours define recovery, reporting, and trust
A company may feel mature because it has strong perimeter controls, a current certification, and a completed supplier review process. But if it cannot identify affected dependencies, assign leadership, preserve evidence, and communicate clearly in the first hours of a third-party incident, that maturity will not hold up under pressure.
The future of supply chain cyber resilience will not be decided by who has the longest vendor questionnaire. It will be decided by who can respond fastest, with the clearest ownership, the best visibility, and the strongest operational discipline when a trusted party becomes the entry point.
Assume breach. Map dependencies. Test supplier scenarios. Build evidence readiness. Strengthen identity controls. Clarify leadership before the crisis. This is the practical baseline for operating in a world where your next cyber incident may start in someone else’s environment but become your problem in minutes.
FAQ: Supply Chain Cyber Risk, Supplier Breaches, and Incident Response
What is a supply chain cyber attack?
A supply chain cyber attack is a cyberattack that targets a trusted third party, such as a software vendor, managed service provider, cloud platform, logistics partner, or other supplier, in order to reach downstream customers or to create wider operational impact. Instead of attacking one organisation directly, the threat actor compromises a supplier that already has access, trust, or integration across multiple environments.
Why are supply chain attacks so dangerous?
Supply chain attacks are dangerous because one breach can affect many organisations at once. A compromised supplier can provide attackers with access to customer data, shared systems, operational workflows, or administrative pathways. These attacks are especially disruptive because they often look like legitimate activity and can spread before the affected organisations fully understand what has happened.
Why are supply chain attacks difficult to detect?
Supply chain attacks are difficult to detect because they often come through trusted channels. The malicious activity may involve a real supplier account, an authorised integration, a legitimate software update path, or a routine business workflow. That means traditional security controls may not immediately flag the activity as suspicious, especially in the early stages of the incident.
What is the difference between a supplier breach and a supply chain attack?
A supplier breach means a vendor or third party has been compromised. A supply chain attack is the broader security event in which that compromise is used to affect customers, partners, or other connected organisations. Not every supplier breach becomes a large scale supply chain attack, but every supplier breach has the potential to create downstream risk if the supplier has trusted access, shared systems, or sensitive data.
How do threat actors get into the supply chain?
Threat actors usually enter through familiar weaknesses rather than exotic techniques. Common entry points include stolen credentials, exposed remote access, poor patching, vulnerable internet facing applications, email compromise, social engineering, and voice phishing. The method is often ordinary. The impact becomes extraordinary because the compromised organisation sits at a strategic point in the supply chain.
What are common examples of supply chain cyber risk?
Common examples include compromised managed service providers, malicious or abused remote monitoring tools, hijacked software update mechanisms, breaches at SaaS providers, fraud through booking or payment platforms, and supplier compromises that expose customer data. Any third party with access to systems, identities, data, or customer workflows can become part of a supply chain risk scenario.
Why are managed service providers a major supply chain risk?
Managed service providers (MSP) are a major supply chain risk because they often have privileged access across multiple customer environments. If an attacker compromises the provider, they may gain a route into many clients at once. This makes MSPs attractive targets for ransomware operators, financially motivated cybercriminals, and other threat actors seeking scale and speed.
Are supply chain attacks mainly caused by software vulnerabilities?
No. Software vulnerabilities are important, but they are only one part of the problem. Supply chain attacks can also involve identity abuse, trusted vendor relationships, weak segmentation, compromised platforms, phishing, voice phishing, and misuse of legitimate access. In many cases, the core issue is not only technical weakness but misplaced trust combined with limited visibility.
Should organisations always install the latest security updates?
Yes, in general organisations should apply the latest security patches promptly, especially for internet facing systems and software that could expose access to attackers. However, patching should not be treated as the end of the response. If a patch fixes a serious vulnerability, organisations should also assess whether compromise may already have occurred between the release of the patch and the moment it was installed.
Is delaying patching safer than using the most recent version of software?
No, delaying security patching usually increases risk rather than reducing it. Older versions often remain vulnerable to known exploits. The better approach is to maintain disciplined patch management, test critical updates efficiently, and perform a compromise assessment when there is a meaningful chance the vulnerability was exploited before remediation.
What is a mass downstream attack?
A mass downstream attack happens when attackers compromise one supplier or shared platform and then use that position to affect many customer organisations at once. This is one of the most serious forms of supply chain cyber risk because it allows a single incident to create widespread operational disruption, ransomware exposure, data theft, or trust collapse across an entire customer base.
What is a targeted supply chain attack?
A targeted supply chain attack happens when attackers want to compromise a specific organisation but decide to enter through one of its suppliers, vendors, service providers, or partners. This approach is often used when the primary target is well defended and the attacker believes a third party offers a weaker or less closely monitored route in.
Why is supply chain cyber risk now a board-level issue?
Supply chain cyber risk is now a board-level issue because the consequences go beyond technology. A supplier breach can disrupt operations, halt production, delay deliveries, trigger reporting obligations, expose sensitive data, damage customer trust, and create legal or regulatory consequences. These are enterprise risks that require executive ownership, not just technical controls.
How can a company tell what data a supplier can access?
A company can determine supplier data access by maintaining an up to date inventory of vendor integrations, shared identities, data flows, connected platforms, and business processes supported by third parties. This should include which supplier has access to which systems, what data they can read or modify, what accounts they use, and how that access is monitored and reviewed.
Why is visibility into supplier access so important?
Visibility into supplier access is essential because it speeds up decision making during an incident. If a supplier is breached, the organisation must quickly understand which systems, accounts, and datasets may be affected. Without that visibility, containment is slower, reporting becomes harder, and business leaders cannot confidently assess operational or regulatory impact.
What should an incident response plan include for a supplier breach?
An incident response plan for a supplier breach should define who leads the incident, who has decision making authority, how to engage the supplier, how to isolate affected systems or access paths, how to preserve evidence, how to assess legal and regulatory obligations, and how to coordinate technical response with internal and external communications. The first hours should be clearly mapped.
How often should a company test its incident response plan for supplier related scenarios?
A company should test its incident response plan for supplier related breach scenarios at least annually, and ideally more often if its supplier landscape is complex or high risk. The most useful exercises are realistic tabletop simulations that include incomplete information, third party dependencies, escalation pressure, and time sensitive reporting decisions.
What does evidence readiness mean in cybersecurity?
Evidence readiness means having the logs, records, telemetry, and data retention needed to investigate a cyber incident properly. In the context of supply chain security, it includes centralised logging, preserved access records, historical visibility, and forensic data that help determine what happened, what data was exposed, and what must be reported to regulators, customers, or partners.
What are the first steps when a supplier is breached?
The first steps are to confirm the supplier relationship, determine whether your organisation is affected, identify connected systems and accounts, review what data or services the supplier can access, activate the incident response structure, preserve evidence, and make rapid decisions on containment. Organisations should avoid waiting passively for the supplier to provide the full picture before acting on their own exposure.
What role does identity security play in supply chain defence?
Many modern attacks rely on valid accounts rather than malware alone. Strong identity controls such as multi-factor authentication, conditional access, privileged access management, and least privilege can reduce the likelihood that a compromised supplier account becomes a route to broader compromise inside the customer environment.
Can compliance frameworks solve supply chain cyber risk?
No. Compliance frameworks can help structure governance, accountability, and documentation, but they do not prevent incidents by themselves. Real resilience comes from operational readiness, tested response plans, visibility into supplier access, strong identity controls, centralised evidence, and the ability to contain threats quickly when something goes wrong.
What should companies look for in supplier cyber readiness?
Companies should look for practical readiness, not only certifications. Important signals include clear incident escalation paths, transparent security ownership, timely patching, strong identity controls, monitoring capabilities, evidence retention, tested incident response processes, and a willingness to engage openly during a security event. The goal is to understand how the supplier would perform under pressure, not only how it scores on paper.
What is the best way to improve supply chain cyber resilience?
The best way to improve supply chain cyber resilience is to combine strong preventive controls with incident readiness. That means mapping supplier dependencies, understanding data access, tightening identity security, applying least privilege, monitoring continuously, preserving evidence, testing supplier related incident scenarios, and defining clear ownership for the first hours of response.
What should executives ask about supplier cyber risk right now?
Executives should ask five practical questions. Which suppliers are operationally critical. Which suppliers can access sensitive systems or data. Would we know quickly if one of them were breached. Is it clear who leads our response. Have we tested that scenario recently. These questions are more useful than generic assurances because they focus on readiness, speed, and accountability.