The audit question nobody prepares for
Incidents are not the only scenario where this matters. Regulators and insurers are asking the same question your security team would ask after a breach. Can you show me what your environment looked like three months ago? Six months ago? Last September?
NIS2 requires organisations to implement appropriate logging and monitoring as part of their risk management obligations. ENISA guidance points to six months as a baseline for essential entities. Cyber insurers are increasingly asking about log retention capability at renewal. None of this maps onto the 14-to-90-day default your endpoint tools are keeping.
The gap is not a technical failure. It is a default setting that nobody changed, because nobody told them it needed changing.
Why the obvious fix doesn't fit
The standard answer to a log retention gap is a SIEM. Deploy it, configure it, staff it, maintain it. Budget six figures. Hire the specialist who knows how to run it.
For a 350-person manufacturer whose IT team of two already handles everything else, that is not an answer. That is a different problem. The cost and complexity of a SIEM was designed for enterprise security teams with dedicated headcount. It was never built for a stretched IT manager who also runs the helpdesk, manages the infrastructure, and fields questions from the CFO about the cyber insurance renewal.
The result is that most mid-sized companies do nothing. The gap stays open. The default settings stay unchanged. And the 90-day window keeps rolling forward, quietly overwriting the record.
What closing the gap looks like
Closing the log retention gap does not require a SIEM. It requires a 12-month log archive that is EU-stored, and accessible when it matters.
When an auditor asks for September, the answer is yes. When an incident investigation needs to reach back six months to understand how a threat entered the environment, the record exists. When the insurance broker asks about log retention at renewal, the box is already checked.
The logs should be there from day one. Retrieval should not require a project. And the team pulling the records should be the same team that detected the threat, not a separate forensics firm brought in after the fact.
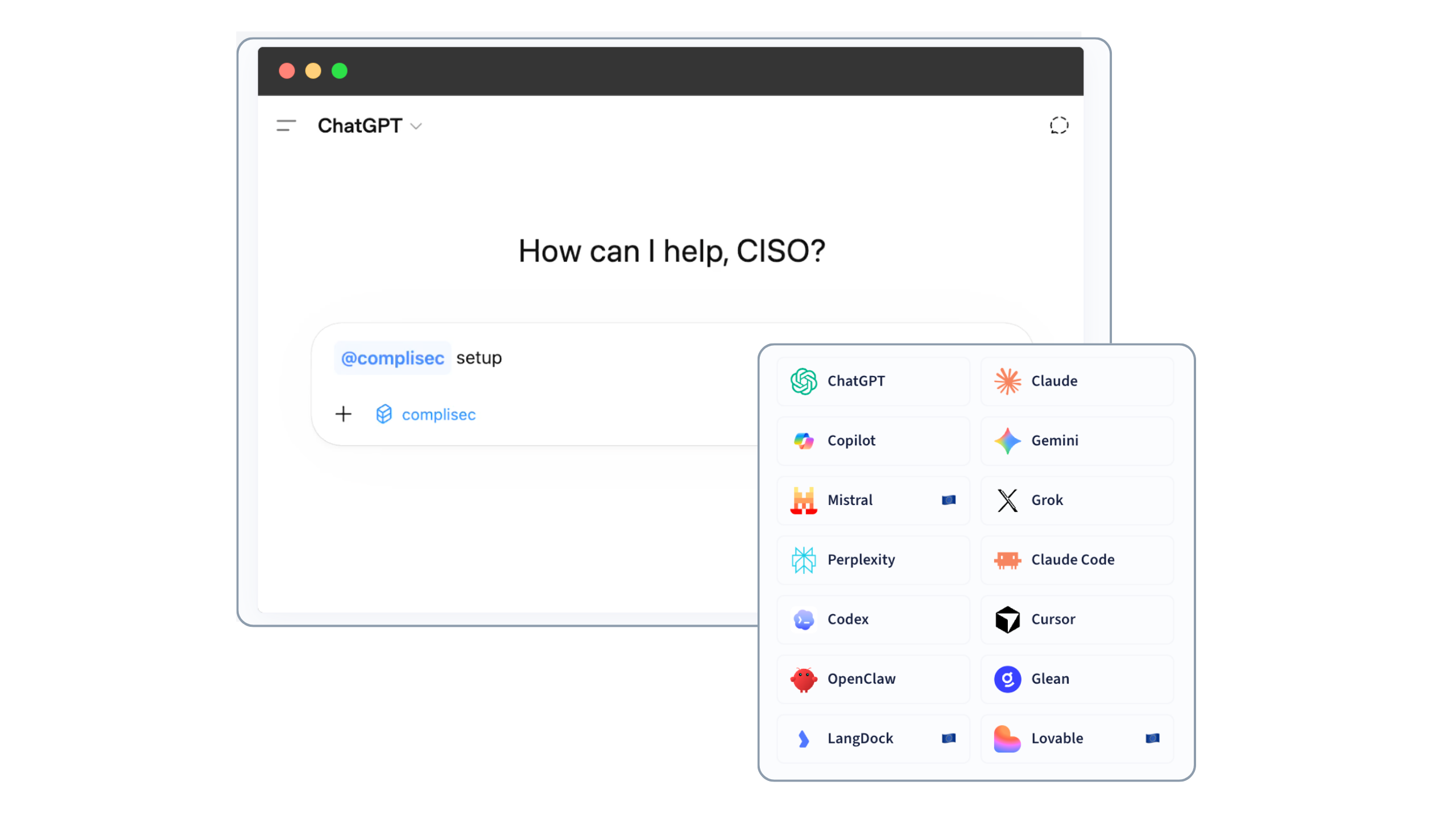
That is why we built Eye Log
Eye Log is a log retention add-on to Eye Cyber Guard. It stores 12 months of logs in EU-based storage.
When the auditor asks, the answer is already there. When an incident needs to reach back further than 90 days, the logs are there and the analysts who need them already have access.
The 90-day blind spot is a default setting. It does not have to stay that way.