Machine learning makes an important contribution to cybersecurity by recognizing patterns in underlying data and thus detecting and preventing possible cyber threats. However, a smart system alone is not enough to secure your company digitally. Human insight and analysis remain necessary.
Machine learning enables computers to recognize patterns in data. This technology has many applications, but one of the most promising ones is cybersecurity. Machine learning in cybersecurity gives computers the ability to detect network intrusions and other dangerous activities that could lead to a data breach. Tijmen Mulder, Incident Response Lead at Eye Security, explains: "Machine learning is a computer model that you can train to recognize things. This requires an enormous amount of training data. The more and the better the data you give the system, the better it can ultimately learn and perform."
How does machine learning work?
You can compare a machine learning model with a baby who cannot walk, cycle, or help around the house immediately after birth. You have to raise a baby and tell them what is right and what is not. This education is also referred to as 'supervised learning' in IT. "People also teach the system what is right and what is not. If you want to teach a model the difference between a cat and a fish, you have to offer it thousands of photos and indicate which photo shows a cat and which one has a fish. In this way, an algorithm learns to make the correct estimate itself," explains Mulder. That estimate is classified, meaning for each photo the system gives a certain percentage of certainty that the image contains a cat or a fish.
There is also 'unsupervised learning'. A large amount of data is offered to the system, and the machine learning module has to remove the deviations. "In this way, the data does not have to be labeled by people, but the model itself will look for differences. In this way, the machine learning system can learn to filter out the odd one out. We also call this 'anomaly detection', or anomaly detection."
What benefits does machine learning offer?
Machine learning is applied in many different areas. For example, in a London hospital, a system was trained to recognize breast cancer. "Thousands of X-rays were loaded into the system and the model was taught which images showed breast cancer and which did not. Subsequently, the system turned out to be better than the radiologists at detecting breast cancer on X-rays," says Mulder. Not only did the system perform better, but it was also able to rate the photos faster, saving a lot of time.
Does machine learning also have drawbacks?
Unfortunately, machine learning still has some limitations. "It is sometimes very difficult for a computer to distinguish things that are obvious to us humans. For example, take a picture of a muffin with blueberries and a picture of a Chihuahua's snout. We immediately see what the dog is and what the muffin is, but a machine learning algorithm can have trouble with this," Mulder smiles. He certainly does not see machine learning as a holy grail, especially because the technology also runs up against practical limits. "A computer model cannot yet be trained to 100 percent accuracy, especially because such a system does not have an infinite amount of data and computing power at its disposal."
Distortion also poses a risk, which is referred to as 'bias' in IT. After all, the system learns from what it is given. "For example, Amazon once tried to use machine learning in application procedures for technical positions. In doing so, the company fed the system with resumes it had received over a decade and learned which resumes had ended up in technical positions. But traditionally, there are often more men in technical positions than women, which led the system to view women as negatively suited."
How does machine learning in cybersecurity help detect threats?
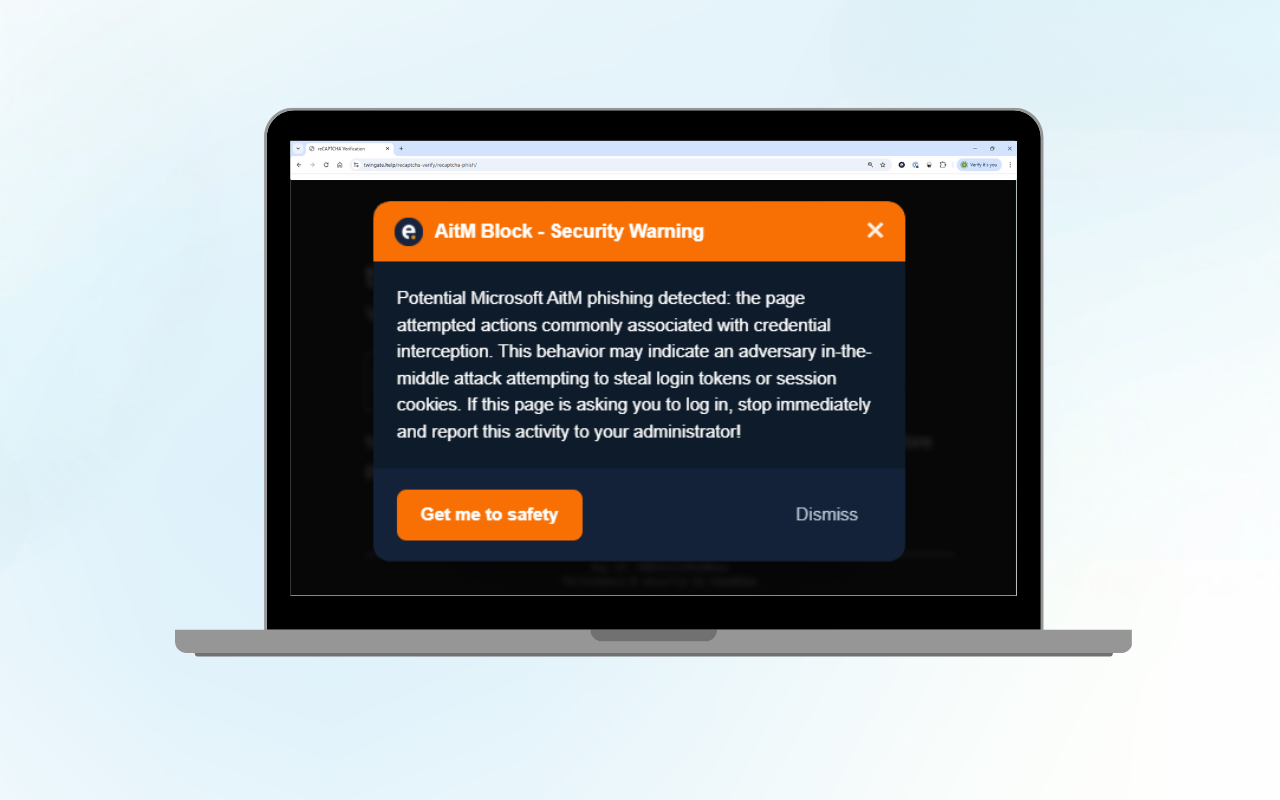
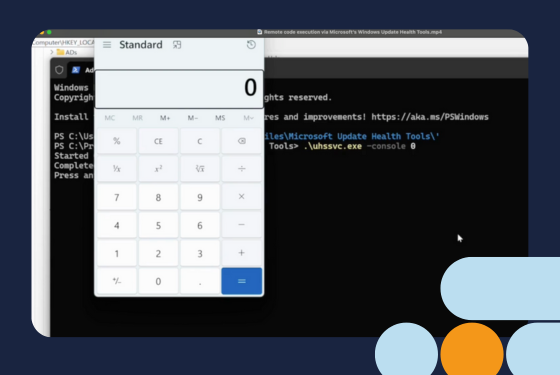
Machine learning is therefore very good at recognizing patterns. A computer can analyze data patterns better than a human, can include more variables in that data analysis, and can do this a lot faster than its human colleagues. Due to this speed and capacity, many processes on computer systems can be scanned for deviations by a machine learning model. The detection of deviations takes place in three different areas, Mulder explains. "First, the model looks at things that are completely different, such as a word processor trying to install another program. A word processor shouldn't install any programs, so when the model encounters this, it sets off an alarm."
The algorithm can also detect contextual anomalies. Then it sends a signal when a user, for example, sends ten emails at once before seven o'clock in the morning. "Sending ten emails at once does not necessarily mean a deviation, but when this happens at an illogical time, it is a cause for alarm." And finally, the module detects collective deviations. "Like when three laptops start up exactly the same process at the exact same time." And therein, according to Mulder, lies the added value of machine learning and cloud computing. "Such a system can analyze all those data points more easily than we humans can. We may be very good at distinguishing Chihuahuas from muffins, but three laptops that start doing exactly the same thing at the same time are likely to escape our attention."
Can I also set this up myself?
Although building and setting up a machine learning model is not rocket science, success stands or falls with the amount and quality of the data collection that is fed into the system. The more data, the more accurate the prediction. For regular companies that do not focus their core activities on these kinds of technical matters, setting up machine learning themselves will therefore not be a priority. "Moreover," says Mulder, "just such a system is not of much use. Because the model can report deviations, but a human expert will always have to look at it to assess whether action needs to be taken. I can imagine that most companies do not have the time, people, or financial resources to handle all those alerts."
The secret of its success lies in the collaboration between the machine learning algorithm and human cybersecurity experts. "The algorithm detects anomalies on the network, after which experts check whether it actually concerns a cyber incident. If that is the case, they can also take immediate action to limit the attack and its effects." The combination of human and machine makes cyber threat detection much more effective and thus increases the protection of your company.
Eye Security uses machine learning in its services and combines it with the expertise of cyber security specialists to increase your resilience. Do you want to know more about our services? Request a no-obligation consultation with our specialists. We are happy to tell you how we can help you increase your cybersecurity.
Frequently Asked Questions about Machine Learning in Cybersecurity
What is machine learning in cybersecurity?
Machine learning in cybersecurity refers to the use of machine learning models and algorithms to identify and mitigate cyber threats. This technology helps in analyzing data patterns, detecting malware, and predicting outcomes to protect digital systems from various cyber risks and future attacks.
How do machine learning models use training data?
Machine learning models rely on massive amounts of training data to learn and improve their accuracy. The data includes benign and malicious samples, which help the models distinguish between normal and suspicious activities, enhancing their threat detection capabilities.
What is the role of artificial intelligence in cybersecurity?
Artificial intelligence (AI) plays a crucial role in cybersecurity by enabling advanced threat intelligence and automated analysis of potential threats. AI-driven cybersecurity systems can detect and respond to emerging threats more quickly than traditional, human-driven detection methods.
How do intrusion detection systems benefit from machine learning?
Intrusion detection systems (IDS) benefit from their machine learning capabilities by using algorithms to analyze user behavior patterns, network systems, and data points to identify anomalies and potential cyber attacks. This enhances the effectiveness of IDS in protecting data and digital environments.
What is the difference between supervised and unsupervised learning in cybersecurity?
Supervised learning involves training models with labeled data to recognize specific types of cyber threats, while unsupervised learning analyzes data without predefined labels to identify unknown or unexpected patterns that could indicate potential cybersecurity threats elsewhere.
How does reinforcement learning contribute to cybersecurity?
Reinforcement learning helps in cybersecurity by allowing models to learn from their actions and improve their decision-making processes to predict outcomes over time. This approach is useful for developing adaptive security systems that can respond to evolving cyber risks and advanced threats.
How can machine learning reduce human error in cybersecurity?
Machine learning reduces human error by automating repetitive tasks, analyzing vast amounts of data, and providing accurate threat detection. This helps security teams focus on addressing more complex issues and reduces the likelihood of missed threats due to human oversight.
What is anomaly detection in machine learning?
Anomaly detection is a machine learning technique used to identify unusual patterns in data that may indicate a security breach or cyber attack. It helps in detecting deviations from normal behavior, enabling early detection of potential threats.
How do machine learning algorithms improve cybersecurity practices?
Machine learning algorithms improve cybersecurity practices by automating threat detection, analyzing historical data, and identifying vulnerabilities. This enables security personnel to proactively address threats, protect data, and enhance overall security measures.